How a blockchain works – the Proof of Work

When we were talking about mining, we mentioned a difficult puzzle that a miner has to solve. What is this puzzle and what is it for?
Before reading this article, I suggest you read these two articles
So what is the puzzle that has to be solved by a miner?
The puzzle that a miner has to solve during the block creation is called proof-of-work. The proof-of-work is a piece of data which requires computational power to be created but it can be verified quickly. Thanks to the proof-of-work the blockchain’s data becomes immutable.
In the previous article we created a simple blockchain and we saw that tampering a block causes the invalidation of the following blocks.
In that example recalculating the hash of invalid blocks is simple, but if we add complexity in the calculation we will make the bad guys’ life difficult.
What is the proof-of-work for? Why do miners spend so much effort on mining?
The proof-of-work is a mechanism for reaching global consensus on the valid blockchain: since all nodes have a copy of the blockchain, each node must agree on the conditions that prove how much effort a node has spent on verifying transactions.
In other words: if the content of the blockchain is easy to change then everyone can tamper with it; instead, if each block is calculated with complex mathematical functions then it takes a lot of effort to tamper with the blockchain.
Let’s check the proof-of-work more in depth.
Let’s create a blockchain where the blocks are linked to each other through an identification code; a block contains the following data:
- identification code of the previous block (PREV)
- name of the sender (SENDER)
- name of the receiver (RECEIVER)
- bitcoin amount (AMOUNT)
To make the calculation difficult, every identification code must start with 0000 (four zeros). To do this we have to add a new field called NONCE.
For a better understanding let’s take an example.
The first block of our blockchain includes the following data (please note that the identification code of the previous block is 0 because this is the first block):
PREV:0
SENDER:john
RECEIVER:jenny
AMOUNT:100
NONCE:1
Now let’s copy this block content, then paste it in the hash calculator and press the button Calculate SHA-256 Hash (be careful with spaces and new lines). The hash is as follows:
07b01b0f4672f2bc58ef11132df4bc74a4e0dc9f2e07ee5d9a0428d3836bc6cb
As you can see the code starts with b273 and not with 0000; so you must increase the NONCE and repeat the calculation again (note that increasing the NONCE from 1 to 2 leads to the change of the content and consequently the hash changes too).
Now our block is:
PREV:0
SENDER:john
RECEIVER:jenny
AMOUNT:100
NONCE:2
and its hash is:
263172553403d3182866ed4d2e7b588a6932e58d0acaa1fa92958a1f70dfabc5
The code still does not start with 0000! You must repeat the calculation all over again until the code starts with 0000. OK, I will give you the solution: you have to repeat this process 22683 times!
PREV:0
SENDER:john
RECEIVER:jenny
AMOUNT:100
NONCE:22683
Hash code: 00000d7d33ebf71c24c15119c925acf9d9d45f8f9972034e2c8b1aabe29163a7
As it was said in the previous article, the hash is a one way function, so the only way to find the block’s identification code that starts with 0000 is making random attempts (the method is called brute force).
Let’s create a blockchain that we made in the previous article but this time we will apply the proof-of-work to it; this is what we get:
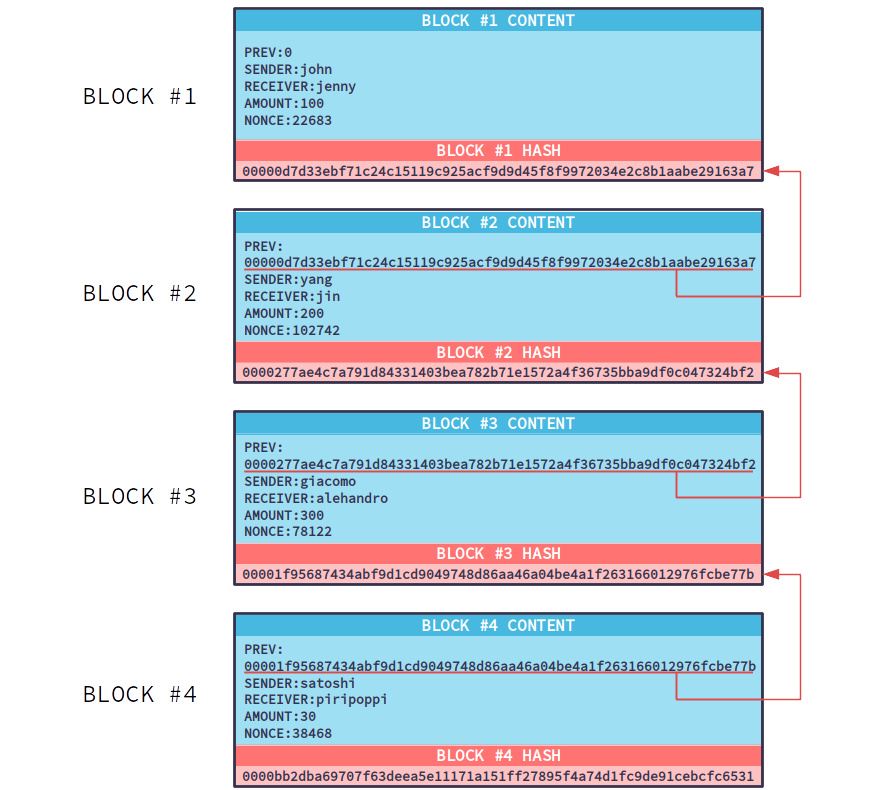
If you tamper the first block, you will break all the blockchain and for every block you will have to calculate the hashes that start with 0000 again! So, when a certain block has many blocks after it, this block becomes secure.
In the bitcoins world a block becomes secure when it has at least 6 following blocks; keep in mind that the difficulty of the hash calculation is much higher than our example.
If you want to tamper the bitcoin’s blockchain, remember that every fake block must comply with the calculation difficulty criteria and moreover you have to create fake blocks faster than the other miners in the network… to achieve this you need 51% of the computational power of the whole network!
Nowadays the blockchain technology is pushing to find other ways to reach the network consensus because the proof-of-work is not energy-efficient at all. Some of these new ways are proof of stake, proof of burn or casper _
More Info
Bitcoin hash rate: https://blockchain.info/it/charts/hash-rate?timespan=all
More info about proof-of-work: https://en.bitcoin.it/wiki/Proof_of_work
HASH calculator: https://www.danielefavi.com/sha256-hash-calculator/
PHP code that I used to create the blockchain example: https://github.com/danielefavi/blockchain-hash-block-calculator